


On April 19, 2026, the AI development platform Vercel disclosed a security incident involving unauthorized access to internal systems and subsequent data theft. The breach wasn’t a direct compromise of Vercel’s infrastructure. Rather, it originated from a compromised third-party tool that had been integrated into corporate accounts. Customer API keys and proprietary source code were stolen. A threat action claiming affiliation with ShinyHunters has since listed the data on a criminal forum with an asking price of $2 million.
Vercel is working with Mandiant and other firms on the investigation. Attribution is still developing, but Vercel has described the attacker as being “sophisticated”, citing the operational speed and detailed knowledge of Vercel’s systems.
The entry point was an AI tool called Context AI. A Vercel employee had connected this tool to their corporate Google account, granting it full OAuth access without IT or security awareness. That connection gave Context AI a persistent token with standing access to the employee’s Google account, no password required.
ContextAI was then compromised via an infostealer malware infection on one of its own employees' machines. That gave ShinyHunters access to Context AI’s AWS environment, where OAuth tokens were stored without encryption (including the one that granted access to Vercel’s Google environment). Attackers easily leveraged the token to break into Vercel systems and move laterally. From there, ShinyHunters was able to access Vercel’s credentials, API keys, and source code, potentially turning it into a jumping-off point for the next breach.

This is the SaaS supply chain attack in its purest form. No phishing. No zero-day. Just a valid credential inherited from a vendor to connect to their 3rd party application.
Once OAuth tokens are issued, they operate in the background. They are quietly authorized by every system they touch, never triggering login alerts, never prompting MFA. In a large enterprise, there can be hundreds of these tokens in circulation, connecting SaaS tools to core systems across Google Workspace, GitHub, Slack, and more.
The fundamental problem is that SaaS platforms extend trust transitively. When you authorize a third-party app, you're implicitly trusting everyone who touches that app's infrastructure, their cloud provider, their developers, their own connected services. Most organizations don't know what they've actually agreed to.
And when something goes wrong, tracing the blast radius is slow. Security teams typically start from scratch: pulling logs, manually cross-referencing which accounts had what connected, trying to reconstruct a picture of what the attacker could reach. By then, the damage is done.
The SaaS supply chain has always carried risk. But as the ecosystem of apps connecting into enterprise environments continues to expand (particularly AI tools, many of which are early-stage products moving fast) the question of what you've let into your environment becomes harder to answer and more important to get right.
What’s harder: tracing down exposure during an actual incident. To every system involved, the token is valid and the connection is authorized. That's the nature of how SaaS platforms extend trust: a valid credential is a valid identity, and a valid identity can do whatever its permissions allow.
Right now:
This week:
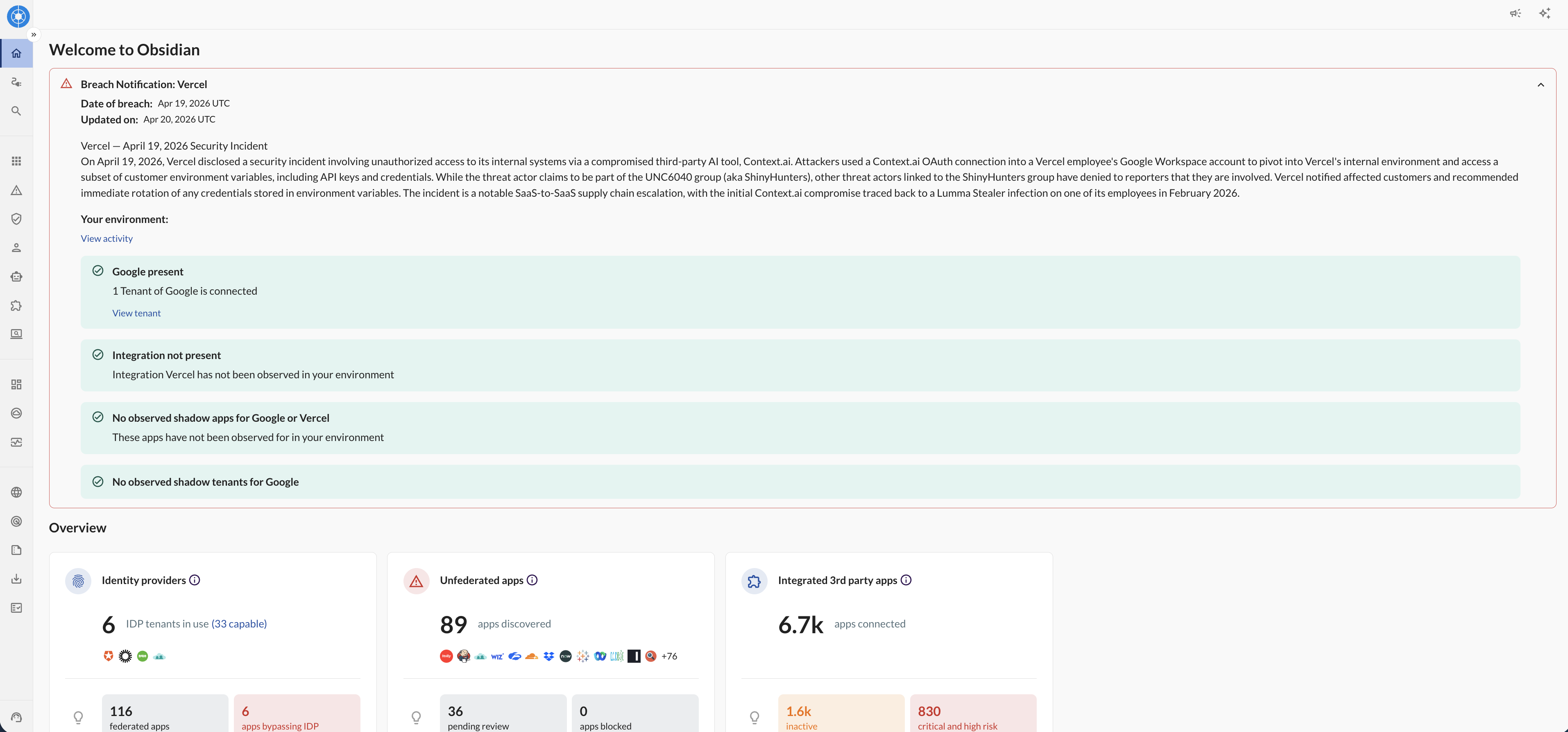
Obsidian customers woke up this morning with answers already in their console, and were able to fast track their incident response.
The Vercel breach isn’t a one-off. It’s a pattern. In the last two years, high-profile SaaS supply chain attacks have hit Okta, Twilio, Cloudflare, Snowflake and now Vercel – all stemming from third-party integrations with standing access to core systems. The attack surface grows every time an employee connects a new tool.
The response most organizations reach for – better employee training, stricter OAuth approval process – helps at the margins. But it doesn't address the core problem: you can't manually track hundreds of OAuth connections, understand what each one can access, and monitor how each one behaves over time. This problem only further exacerbates with the adoption of AI agents.
Traditional solutions don't discover these integrations, can't evaluate their permissions, and have no visibility into the cross-app activity that happens between connected systems. But that’s increasingly how attackers are escalating access and moving laterally.
What defense actually looks like is knowing, at any moment, which third-party apps are connected to your environment, what those connections can reach, and whether they're behaving normally. Not after an incident. All the time.
At Obsidian, we’ve been focused on providing security teams a unified view of every OAuth application, token, and permission across their enterprise app environment (including shadow integrations like Context AI that may be connected without IT awareness). For every integration, you get a living model that tracks how access and behavior change over time.
When a third-party integration is implicated in an incident, Obsidian delivers immediate blast radius clarity: which accounts are connected to the compromised tool, what those accounts can reach, and where suspicious activity is occurring. Instead of starting an investigation from scratch, your team starts with full context.
Start in minutes and secure your critical SaaS applications with continuous monitoring and data-driven insights.