

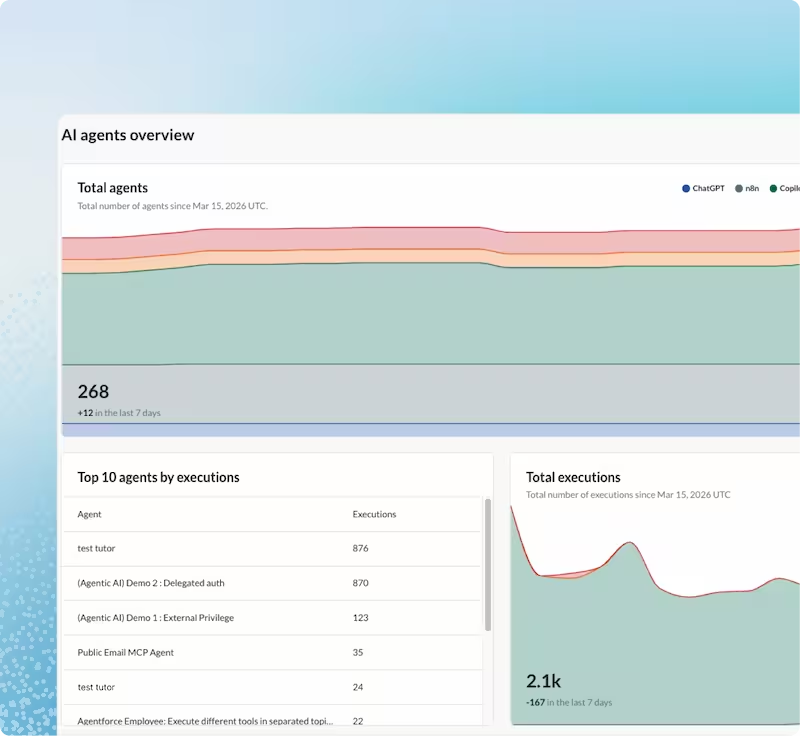
Discover all agents across your enterprise, observe what they can do, and stop high-risk actions at runtime, before damage is done.
Agents inherit permissions, touch real data, and run autonomously across every team, application and platform. The exposure is already there. Most organizations just haven't measured it yet.
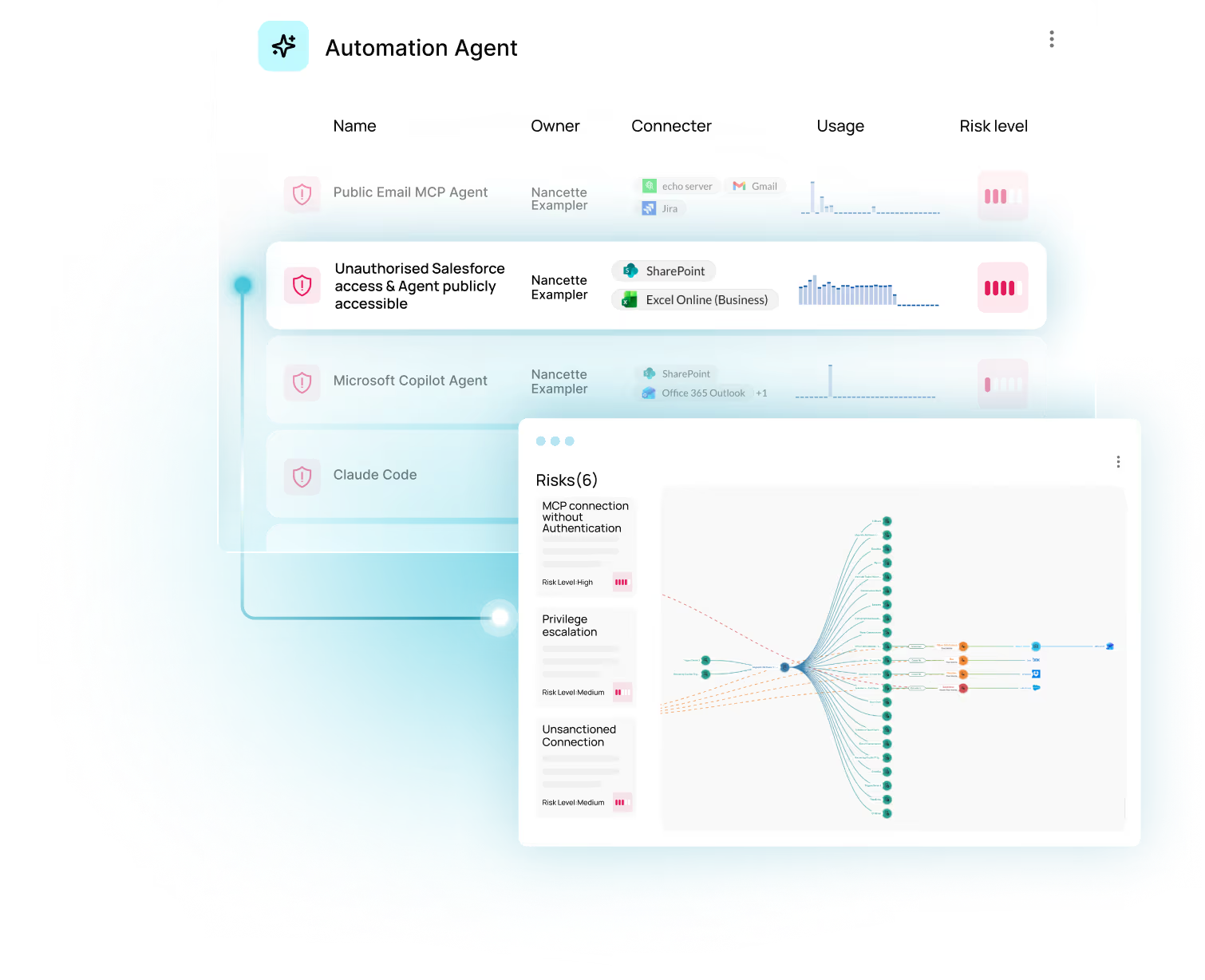
Most tools stop at discovery. Obsidian goes further, showing what each agent can reach, what it's actively doing, and enforcing the controls to stop high-risk actions the moment they occur, not after the fact.
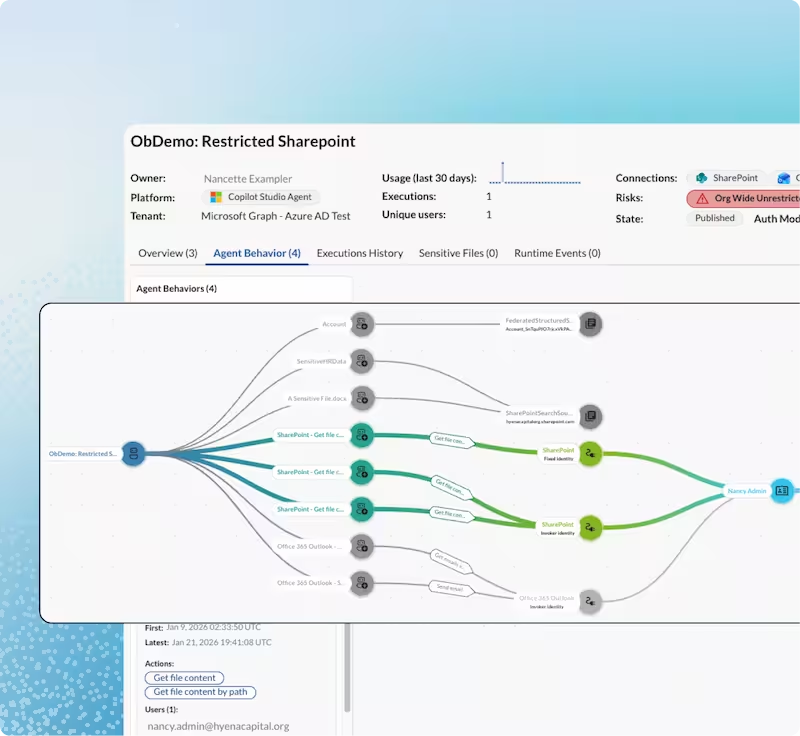
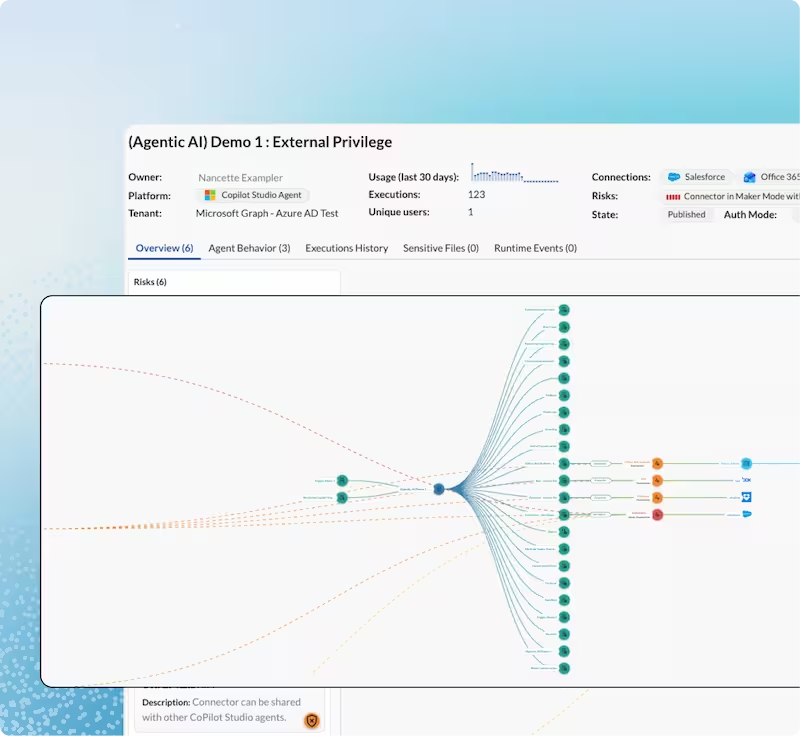
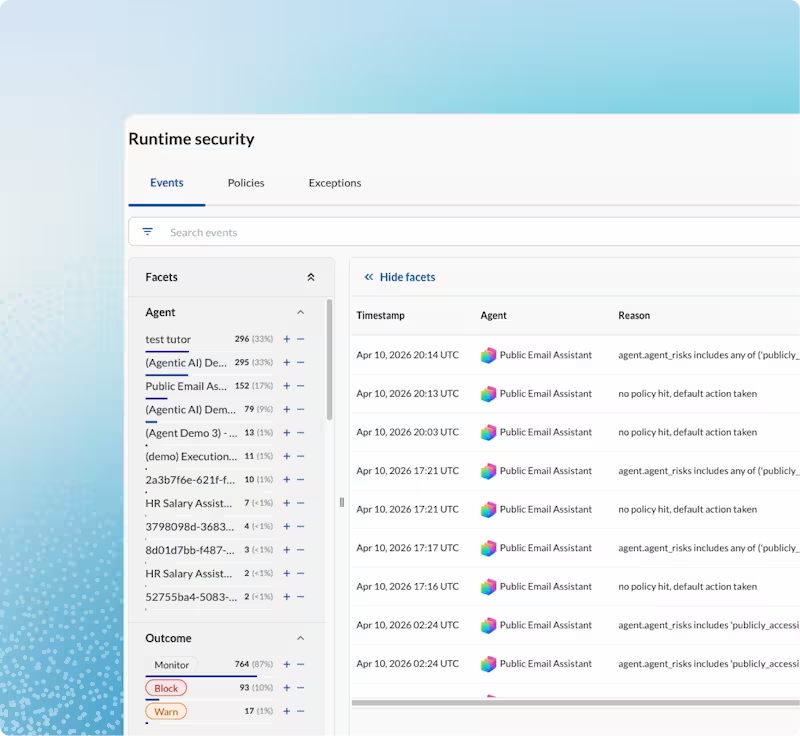
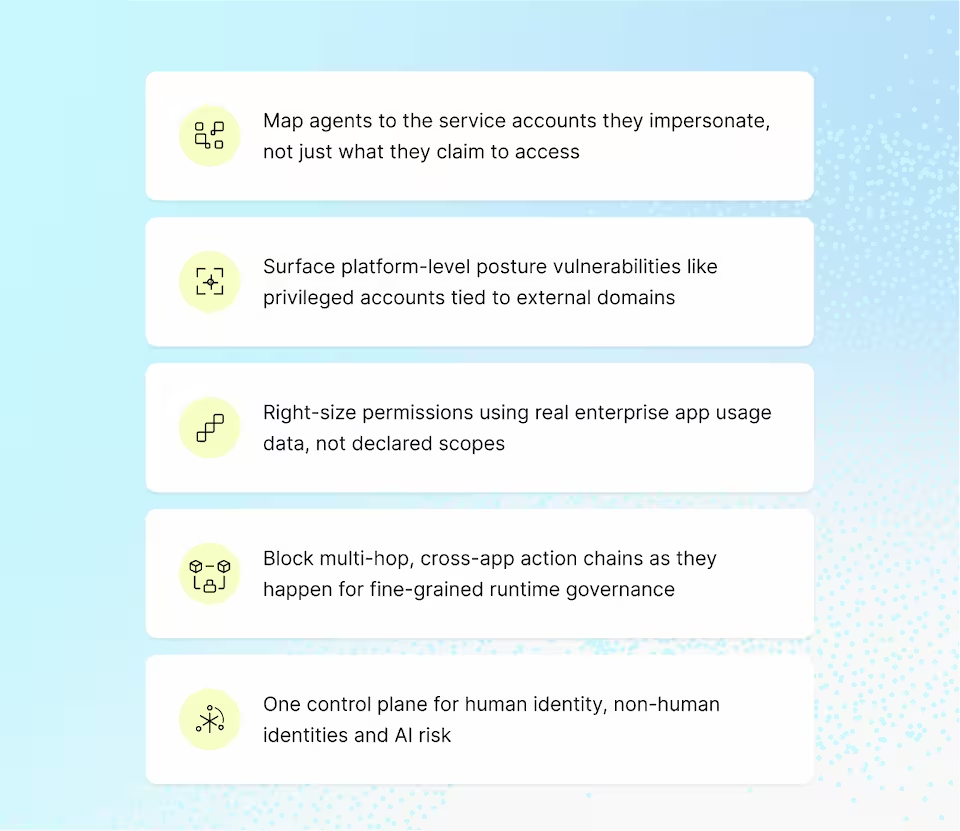
Connecting an agent’s identity to the real service accounts it runs as, the MCP servers it connects through, the actual permissions it holds, and the actions it’s taking right now is what makes end-to-end runtime security and governance possible.
Start with visibility. Add governance. Enforce at runtime. Each stage builds on the last, so your security program grows as fast as your AI footprint does.
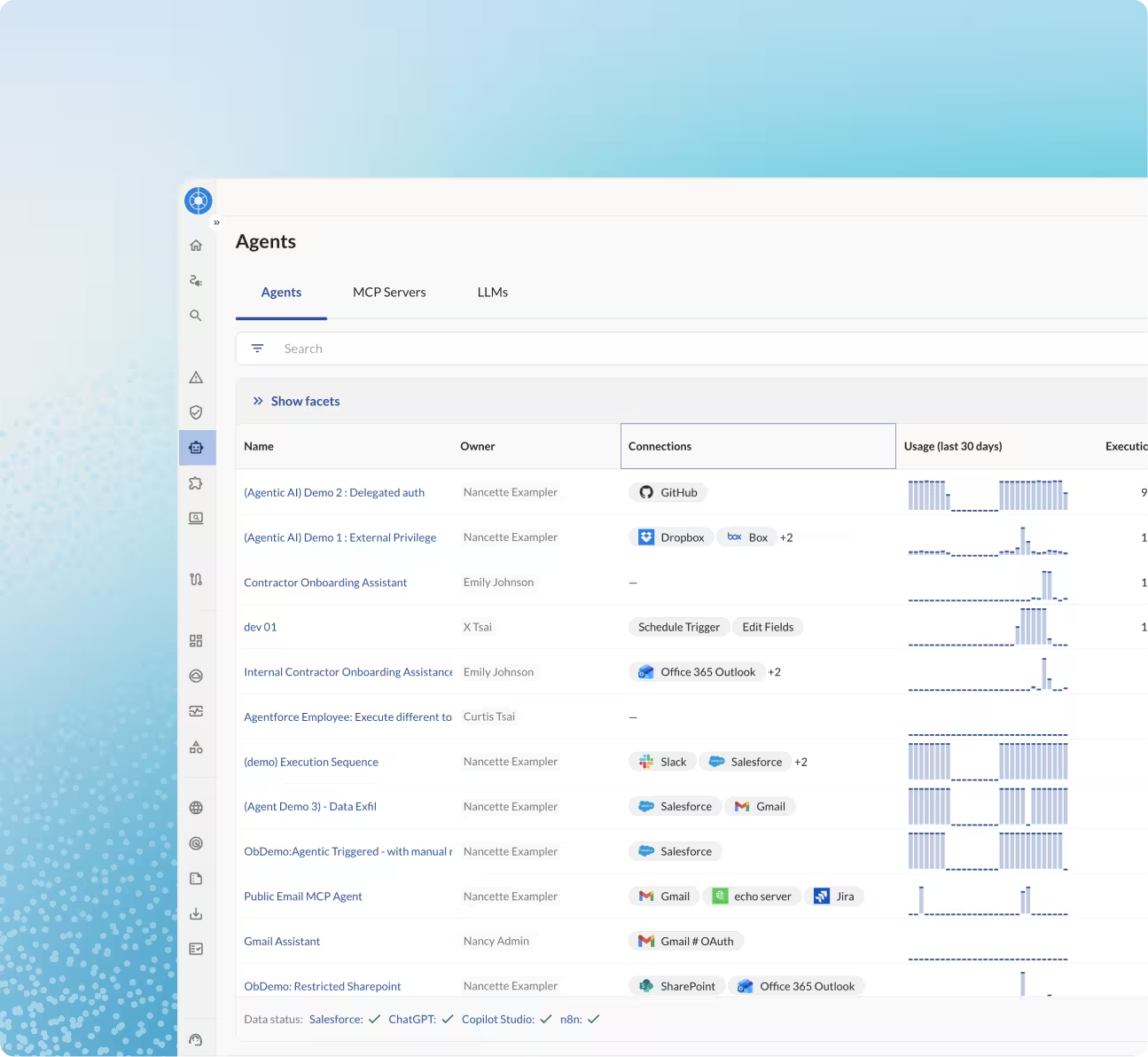
Instantly access out-of-the-box integrations with all major agent platforms across SaaS, cloud, endpoints, and code, so you can get full visibility and governance within hours.


AI agents move data at machine speed, transferring up to 16× more data than traditional SaaS integrations and often inherit 10× more permissions than they need. This explosion creates hidden pathways for misuse. If compromised, an agent can exfiltrate sensitive data or spread across systems in seconds, introducing new supply chain risks.
No. Traditional SaaS integrations usually have narrow, well-defined scopes. AI agents are different: they chain tasks across multiple apps, inherit broad OAuth privileges, and act on behalf of users without human approval. That autonomy makes them far more dangerous if left unchecked. The longer you wait, the faster the risks multiply.
SaaS applications are deeply interconnected, and AI agents amplify this by chaining actions across multiple platforms with little oversight. If one agent is compromised, attackers can pivot into other SaaS systems like Salesforce, Google Workspace, Slack, or Azure in minutes. AI agents expand the attack surface, creating an entirely new class of SaaS supply chain security risks where exposure in one application can rapidly cascade across the enterprise.
SaaS-to-SaaS connectors pass data based on predefined rules. AI agents go further: they make decisions, execute actions across multiple apps, and often request excessive OAuth scopes. Their autonomy gives them far greater reach, making them a powerful accelerant for SaaS supply chain risks if abused.
Very quickly. Thousands of agents can appear in a matter of days. Some are auto-provisioned in seconds. Most launch without IT or security oversight. Left unchecked, these “shadow agents” spread silently, multiplying SaaS connections before anyone knows they exist. Obsidian provides visibility and control directly inside SaaS before that happens.
No. Legacy tools were designed for human-driven SaaS activity, not AI agents. They can’t see agent actions, connect them to OAuth privileges, or enforce least privilege in real time. Agents operate faster, with broader access, and create new supply chain risks that legacy tools can’t detect.
Obsidian gives security teams full visibility into every AI agent, its privileges, SaaS connections, and actions, so you can govern access, stop privilege creep, and prevent misuse before it causes cascading risk. All monitoring and enforcement happens directly inside SaaS in real time, even for low-code/no-code platforms, keeping workflows safe and policy-aligned without slowing innovation.
No. Obsidian protects autonomous workflows directly inside SaaS. Guardrails run in real time, so teams can continue working and innovating safely.