


Okta and other industry reporting first described this 2026 campaign, characterized by voice phishing, account takeover, MFA manipulation, broad SSO enumeration, and downstream data theft. Through customer incident response, cross-customer threat hunting, and analysis of suspicious Okta authentication, MFA enrollment, and post-authentication activity, Obsidian Security identified additional technical details that expand visibility into the actor’s tradecraft. Across observed incidents, the pattern was consistent: compromise an Okta account, establish persistence through MFA changes, pivot across SSO-connected applications, and steal data.
These techniques are consistent with publicly reported ShinyHunters-linked activity and overlap with Scattered Spider–style tradecraft. They also reinforce a broader defensive lesson: effective detection must extend across SaaS applications and correlate activity at the identity layer. Viewed in isolation, suspicious Okta logins, MFA enrollment changes, bursts of SSO activity, and high-volume file downloads may each appear low-confidence. Correlated across a single identity’s activity across SaaS, however, they reveal a clear account takeover and data theft sequence—an area where Obsidian Security is uniquely strong.
The campaign is notable for three recurring elements:
While some variation in Okta event sequences is normal, legitimate user sign-in patterns typically remain relatively stable. In contrast, the incidents described below featured prolonged, failure-heavy authentication chains that deviated sharply from each user’s established baseline.
Attackers gained initial access to the victim’s Okta account through what is most likely voice phishing, as reported by Mandiant. The authentication activity differed substantially from the organization’s normal Okta sign-in flow.
Under normal conditions, Okta authentication commonly follows a relatively predictable sequence, such as:
policy.evaluate_sign_onuser.authentication.verifyuser.authentication.sso or app.auth.ssoapp.oauth2.authorize.code and related OIDC events, where applicableAlthough failed MFA attempts or minor event-order variation may occur, the general structure of a user’s authentication flow usually remains consistent. In this incident, the sequence was highly anomalous and included repeated failed attempts prior to eventual success. This pattern is consistent with phishing activity and aligns with public reporting that threat actors can modify phishing pages and scripts in real time while attempting to complete a victim login.
Observed event progression included repeated cycles of:
policy.evaluate_sign_onapp.ad.login.bad_passwordcore.user.factor.attempt_failcore.user_auth.login_failedThese failures were then followed by a longer successful sequence, including:
policy.evaluate_sign_onapp.ad.login.successcore.user.factor.attempt_successcore.user_auth.login_successuser.authentication.auth_via_mfauser.authentication.verifyapp.oauth2.authorize.code_successapp.oauth2.token.grant.id_token_successThe full authentication flow unfolded over approximately 10 minutes, making it materially longer and more failure-prone than the user’s normal sign-in behavior.
After access was established, the attacker added a new MFA method: Okta FastPass. The device used during FastPass enrollment was an emulated Android device named “Passkey.”
Obsidian determined the device was emulated based on the associated user agent, which included:
com.okta.android.auth/8.19.0 ... Android/16 ... Genymobile/Phone
Genymobile is associated with Android emulation, making this artifact a potentially valuable detection signal when correlated with suspicious authentication activity.
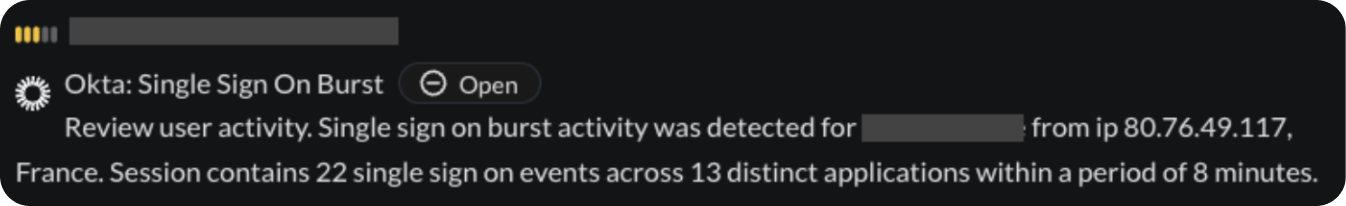
Obsidian generated an SSO Burst alert, indicating the compromised session accessed an unusual number of SSO-connected applications or services in a short period of time. This behavior is consistent with previously observed ShinyHunters and Scattered Spider-attributed activity, where the actor rapidly enumerates accessible applications to determine where sensitive data or privileged workflows may be available.
In this case, the downstream services accessed by the attacker were not connected to Obsidian, limiting visibility into post-pivot activity. However, the observed pattern strongly suggests the actor was validating the blast radius of the compromised identity and searching for high-value data sources.
Obsidian observed a second incident tied to the same campaign cluster. The activity shared multiple tactical similarities with Incident 1, suggesting a repeatable intrusion workflow rather than isolated compromise.
Initial access occurred through a similarly unusual Okta authentication sequence marked by repeated authentication anomalies and an abnormal sign-in pattern.
Following successful authentication, the attacker again enabled Okta FastPass using an emulated Android device named “Passkey.” The emulation platform was once more identified as Genymobile, reinforcing the possibility that Genymobile-linked FastPass enrollment may serve as a useful campaign-level signal when paired with suspicious identity activity.
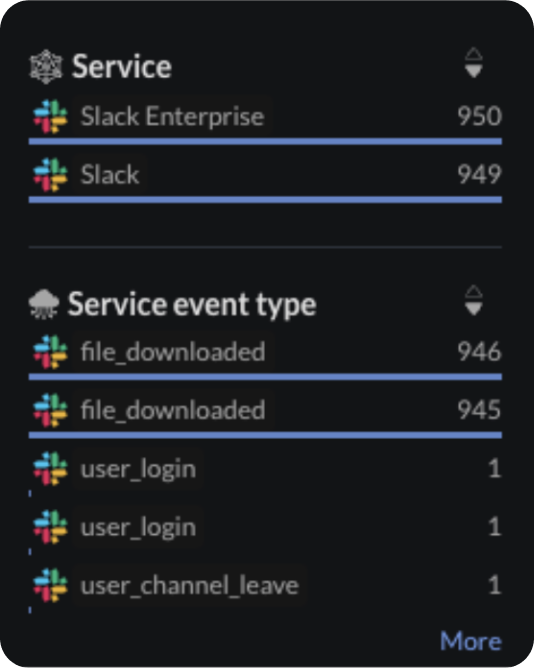
Unlike Incident 1, where post-authentication activity outside Okta was not directly observable, Incident 2 included notable activity in Slack.
First, the compromised account left the organization’s security Slack channel. This action is notable because it may reflect an attempt to reduce visibility, evade internal reporting, or delay detection by preventing the user from immediately seeing security-team notifications or response guidance. The effort was only partially effective: the user rejoined the channel within minutes.
More significantly, the attacker initiated a high volume of Slack file downloads. Files were downloaded within seconds of one another, a pattern strongly suggestive of automated collection and exfiltration rather than ordinary interactive browsing. No decisive artifacts in the event details or user agent clearly identified the automation method, but the speed and volume of collection indicate purposeful bulk theft.

A third suspected incident was discovered during a cross-customer threat hunt for related indicators and alert patterns. The intrusion began in much the same way as the first two incidents, with a highly unusual Okta authentication sequence indicative of phishing-enabled account takeover.
During the authentication activity, Okta Verify associated with a device named “Passkey” was again observed. In this case, however, the user agent did not clearly indicate a known emulation platform, suggesting the actor may vary tooling while preserving similar naming conventions and MFA-enrollment workflows.
Multiple alerts triggered during the intrusion, including:
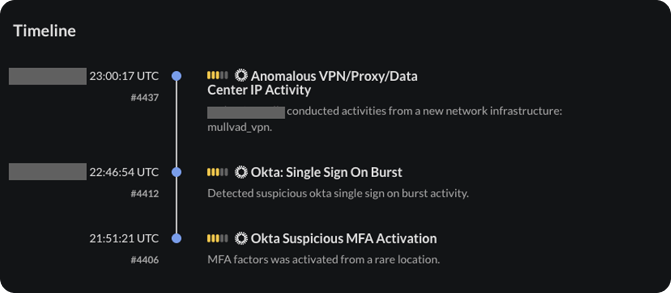
Whereas prior incidents relied primarily on residential and mobile IP infrastructure, this incident also featured VPN and other hosted IP usage, increasing overall confidence that the activity was malicious and not attributable to unusual but legitimate user behavior.
Consistent with the prior incidents, the attacker moved quickly from Okta into additional SSO-connected services.
The compromised identity was used to access a corporate VPN, and an attempted pivot into Salesforce was observed but was unsuccessful.

The attacker then accessed Google Drive, where they downloaded an extremely large volume of files over approximately 90 minutes. This activity is consistent with large-scale cloud data theft following identity compromise.

These incidents reflect a repeatable intrusion pattern centered on identity compromise, MFA persistence, SSO expansion, and data theft. Even when the immediate objective appears to be information theft rather than destructive action or extortion, the operational sequence is significant because it provides a clear path to broader compromise if the actor reaches privileged users, administrative consoles, or third-party integrations.
Defenders should pay particular attention to the following signals and IOCs:
com.okta.android.auth/8.19.0 ... Android/16 ... Genymobile/PhoneTaken together, these incidents show that the actor is not solely dependent on supply chain access. The same operators, or at minimum the same tradecraft cluster, remain capable of achieving meaningful impact through targeted voice phishing and post-authentication cloud abuse alone.
Start in minutes and secure your critical SaaS applications with continuous monitoring and data-driven insights.