


Supply chain attacks that exploit unmonitored SaaS-to-SaaS integrations affect ten times more companies than traditional credential-based breaches.
Obsidian Security’s researchers are tracking the largest SaaS breach campaign of the year, impacting over 700 companies and counting. In new findings, the team has discovered that both Salesforce and Gmail instances have been compromised through the current UNC6395 attack. This is not the first Salesforce breach we’ve observed: earlier this year, threat actors such as Shiny Hunters and Scattered Spider targeted companies through SFDC help desk social engineering. But this attack is different. By exploiting a third-party integration, hackers have amplified the scale and impact of the breach by 10x.
Most victims are technology and software firms themselves, meaning any one of them could trigger a cascading supply-chain breach. This represents a seismic risk for any company using SaaS integrations that bypass proxy and access controls by default.
On August 26th, 2025, Mandiant reported Salesforce breaches via the Salesloft–Drift integration, attributing the activity to UNC6395. Obsidian’s research has independently revealed that the blast radius is even larger than initially reported, with attackers also exploiting the Drift integration into Gmail.
There is additional evidence that this campaign may have been carried out by the combined forces of ShinyHunters and Scattered Spider, as reported by Databreaches.net and Bleeping Computer.
Attackers initially compromised the third-party sales tools Salesloft Drift and Drift Email. They then leveraged these integrations’ identities to pivot into the Salesforce and Google Workspace instances of numerous downstream companies.
It’s currently unclear how far the intrusion extends.

Obsidian Security has been tracking Salesforce attacks before, but these tactics are new.
SaaS breaches have surged recently, impacting companies such as Google, Workday, Cisco, and LVMH. Behind these attacks are ShinyHunters and Scattered Spider in collaboration, a merger Obsidian researchers confirm through trusted sources in direct contact with ShinyHunters leaders (Read more here).
In previous incidents, the combined ShinyHunters–Scattered Spider force relied on phishing, helpdesk social engineering, and leaked credentials to gain initial access to Salesforce instances. In this case, rather than targeting individual Salesforce accounts, attackers focused on Salesloft—the SaaS vendor itself—to pivot into its customer base. Obsidian research indicates that this supply chain approach impacted ten times more organizations than earlier Salesforce breaches.
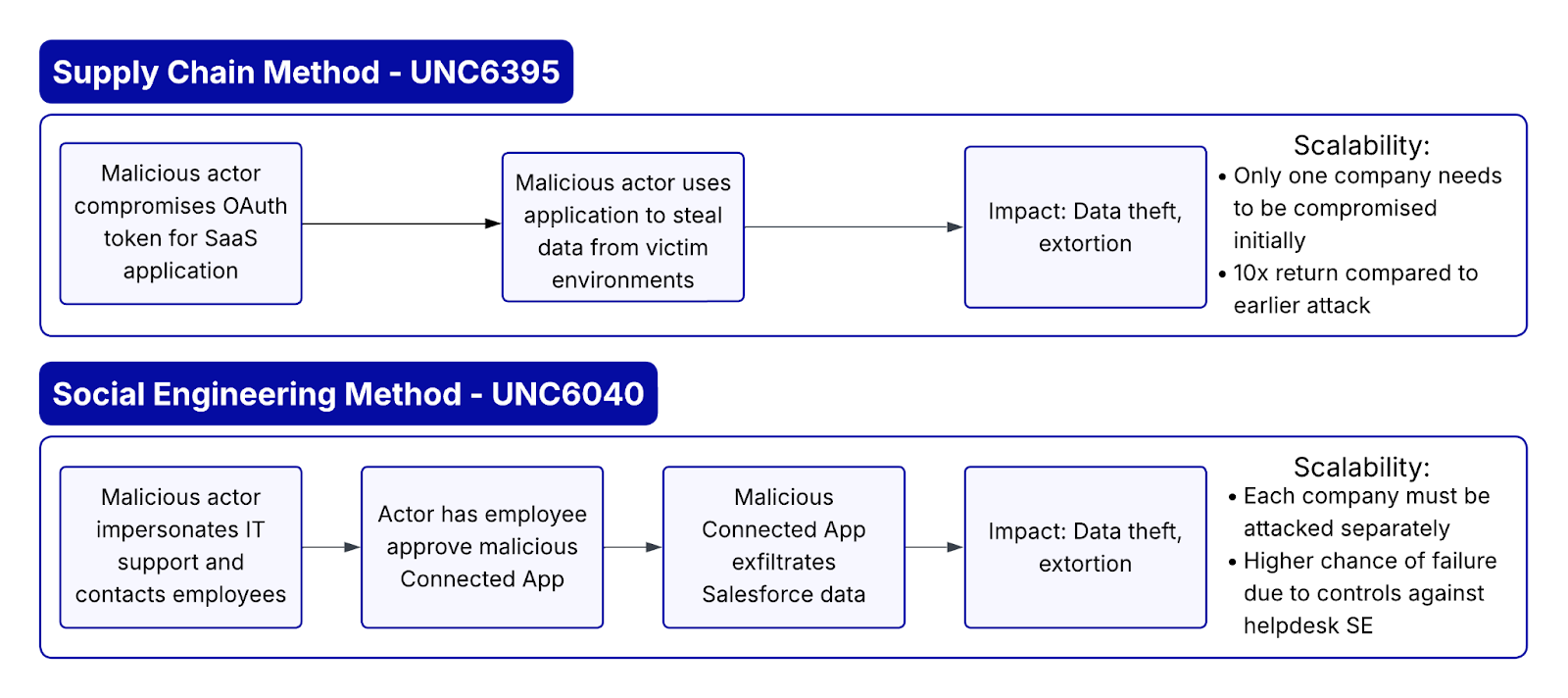
Supply chain attacks are particularly dangerous because attackers don’t target just one company—they compromise a single trusted supplier to gain access to all of its customers. When a vendor is breached, the impact can scale rapidly, potentially affecting hundreds or even thousands of organizations almost instantly.

In previous incidents, attackers need to compromise individual Salesforce instances of each customer.
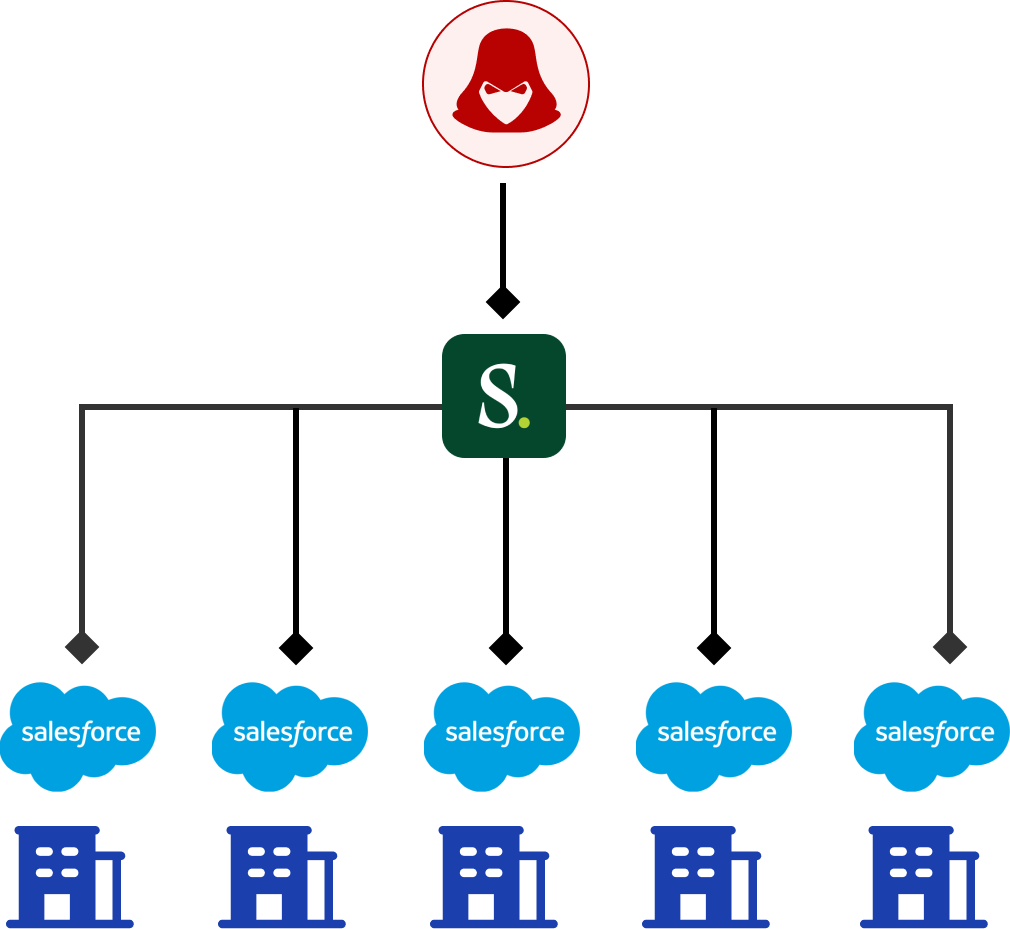
By attacking further up in the supply chain, they only need to compromise one vendor (Salesloft) and then utilize its integrations with Salesforce. This allows them to move downstream and easily infiltrate many more victim orgs.
We’ve seen attacks like this before. In the Okta 2023 support incident, an attacker exploited access to Okta’s customer support system and in turn, put many of its enterprise customers at risk. This Salesloft breach follows the same pattern.
Google has provided several IOCs. Obsidian has discovered an additional one.
The application ID of Drift Email within Google Workspace is http://1084253493764-ipb2ntp4jb4rmqc76jp7habdrhfdus3q.apps.googleusercontent.com/
This is not the first Salesforce-related attack we have tracked this year and it will not be the last. Threat actors increasingly target third-party SaaS applications because they remain a significant blind spot for most organizations.
Securing a single SaaS platform in isolation is not enough. Once attackers gain a foothold, they rarely stop there. They move laterally through connected applications and integrations. This lateral movement makes enterprise-wide visibility and a comprehensive baseline across all SaaS environments essential for detecting and containing attacks.
Organizations should apply the same rigor to SaaS environments as they do to other critical systems. Key measures include:
Want to Learn More? Read more on Obsidian’s investigation into the 2025 Salesforce attacks, where ShinyHunters and Scattered Spider leveraged social engineering, malicious OAuth apps, and voice phishing to access sensitive CRM data. Learn actionable steps to detect threats, respond effectively, and secure your SaaS environment.
Start in minutes and secure your critical SaaS applications with continuous monitoring and data-driven insights.