

Most security tools analyze at the surface-level. We go deeper to give you context and intelligence no one else can.

Over 200 integrations into SaaS and AI applications pull posture and activity data, not just surface-level logs. Go beyond what’s been configured, and see how access is actually being used.

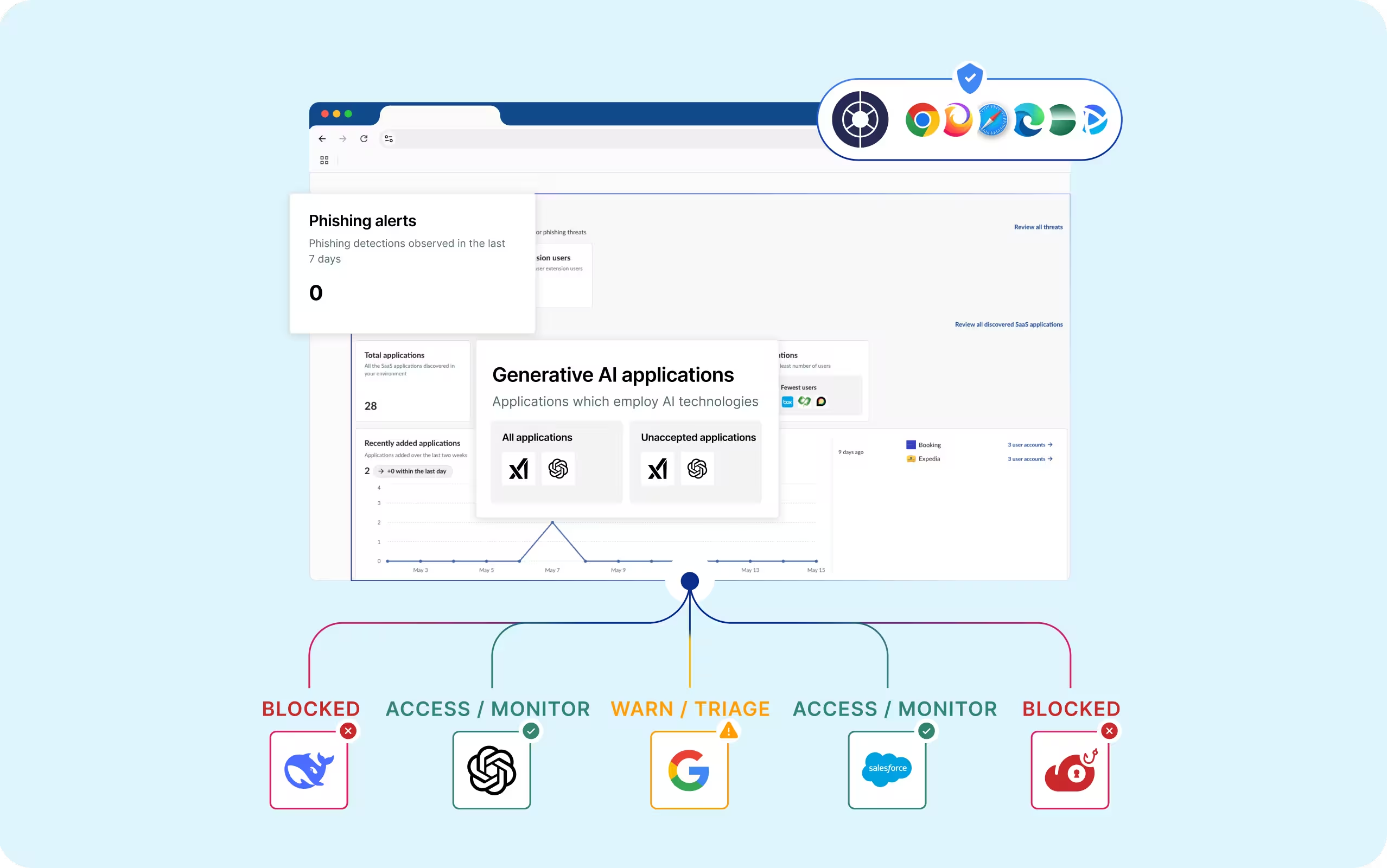
Our browser extension captures real-time user and AI agent activity, confirming what actually happened, not just what server APIs reported. Surface shadow AI, local account use, and session anomalies that admin consoles never see.
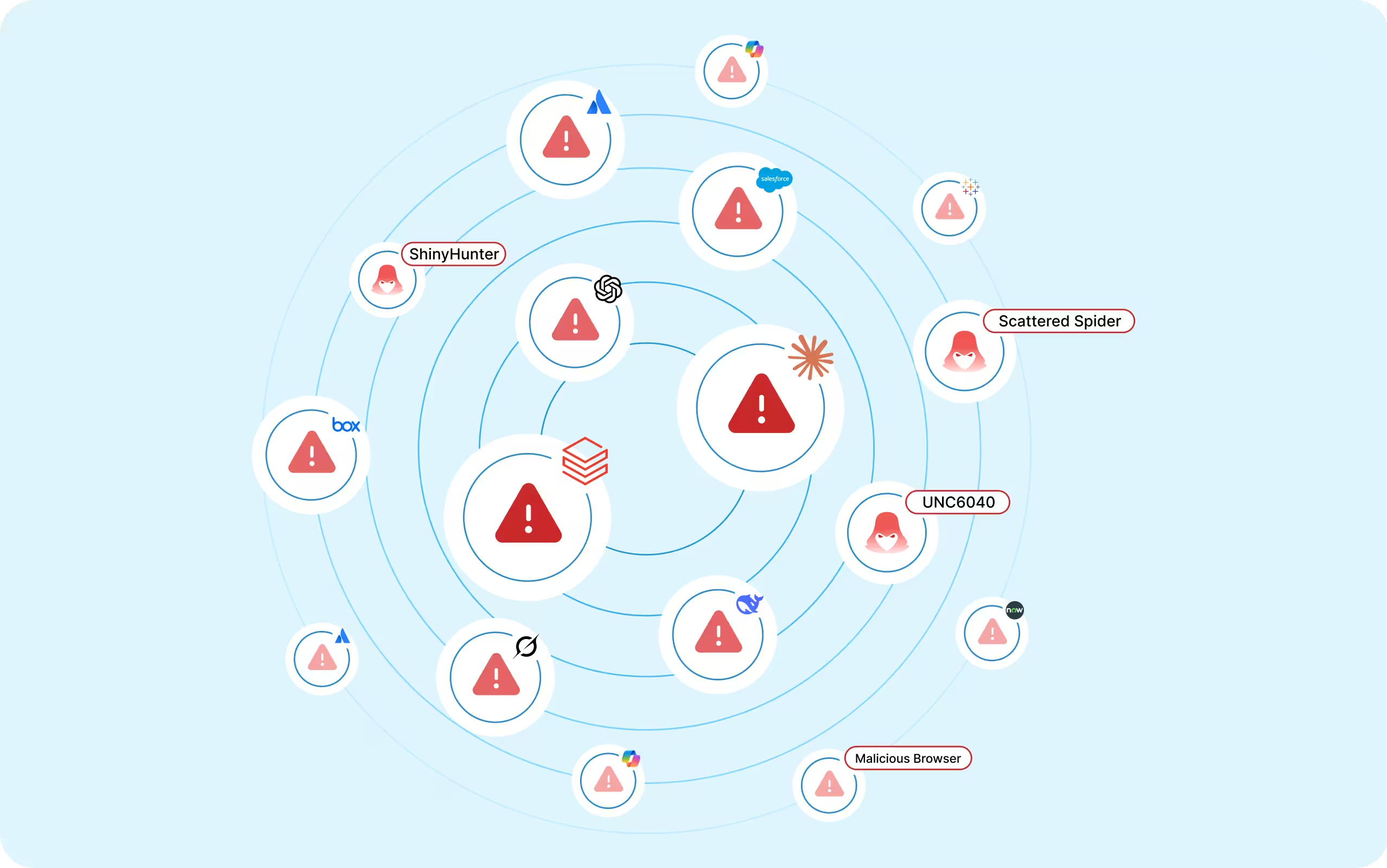
Because attackers don’t follow a static playbook, neither do our detections. They’re built from how attackers actually acted, across 500+ real breach responses with the world's leading DFIR firms. Every breach we investigate sharpens defenses across the environments we protect.
App-integration telemetry, in-browser activity, and real-world breach intelligence power models to continuously improve threat detection and response across the enterprise application stack.
Every human and non-human identity, entitlement, access, and action is normalized and connected in a knowledge graph to provide real-time context and always-on intelligence.
We draw on intelligence across the largest SaaS deployments in enterprise environments, processing over 29 billion events every month, to surface insights and protect customers in our network.
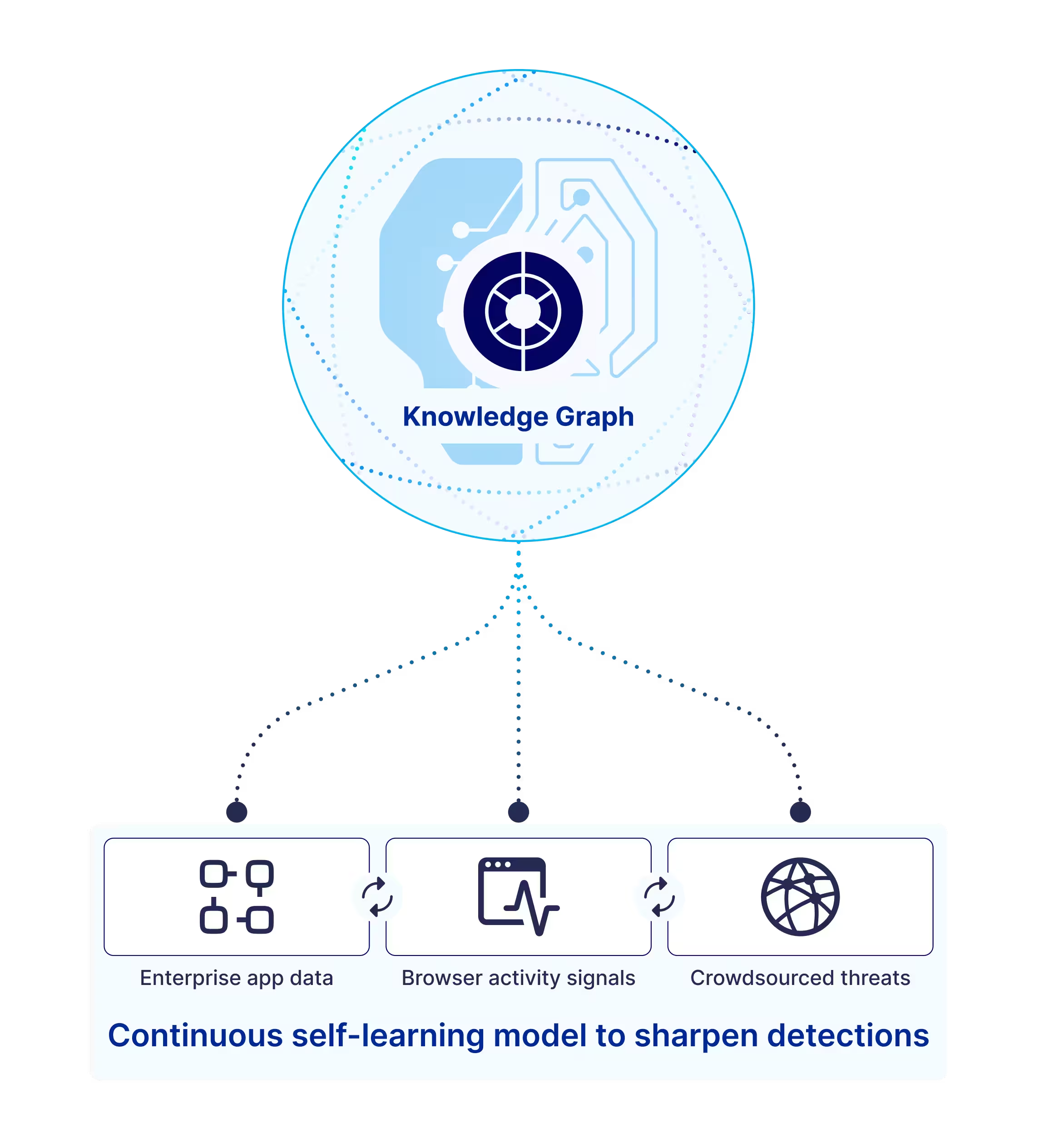
Raw data doesn't reveal risk. Risk lives in the relationships between identities, permissions, and actions. The Obsidian Knowledge Graph is purpose-built to map those connections.

Every user, group, role, entitlement, action, and authentication event is versioned over time, so behavior can be replayed across vendors and nothing is ever overwritten.

Machine learning builds baselines from real enterprise behavior, continuously refined by what we learn from actual incidents.

Configuration, policy, and ownership data is layered together to surface misconfigurations and privilege overlaps. Each finding includes the evidence path and the smallest action needed to remediate.

Service accounts, API tokens, OAuth clients, and AI agents are modeled as first-class entities, with origin, scope, and observed usage, so automation never quietly exceeds its intended role.

Browser telemetry fills the gaps that server APIs miss: confirming authentication strength, exposing local account activity, and detecting session movement that signals active compromise.
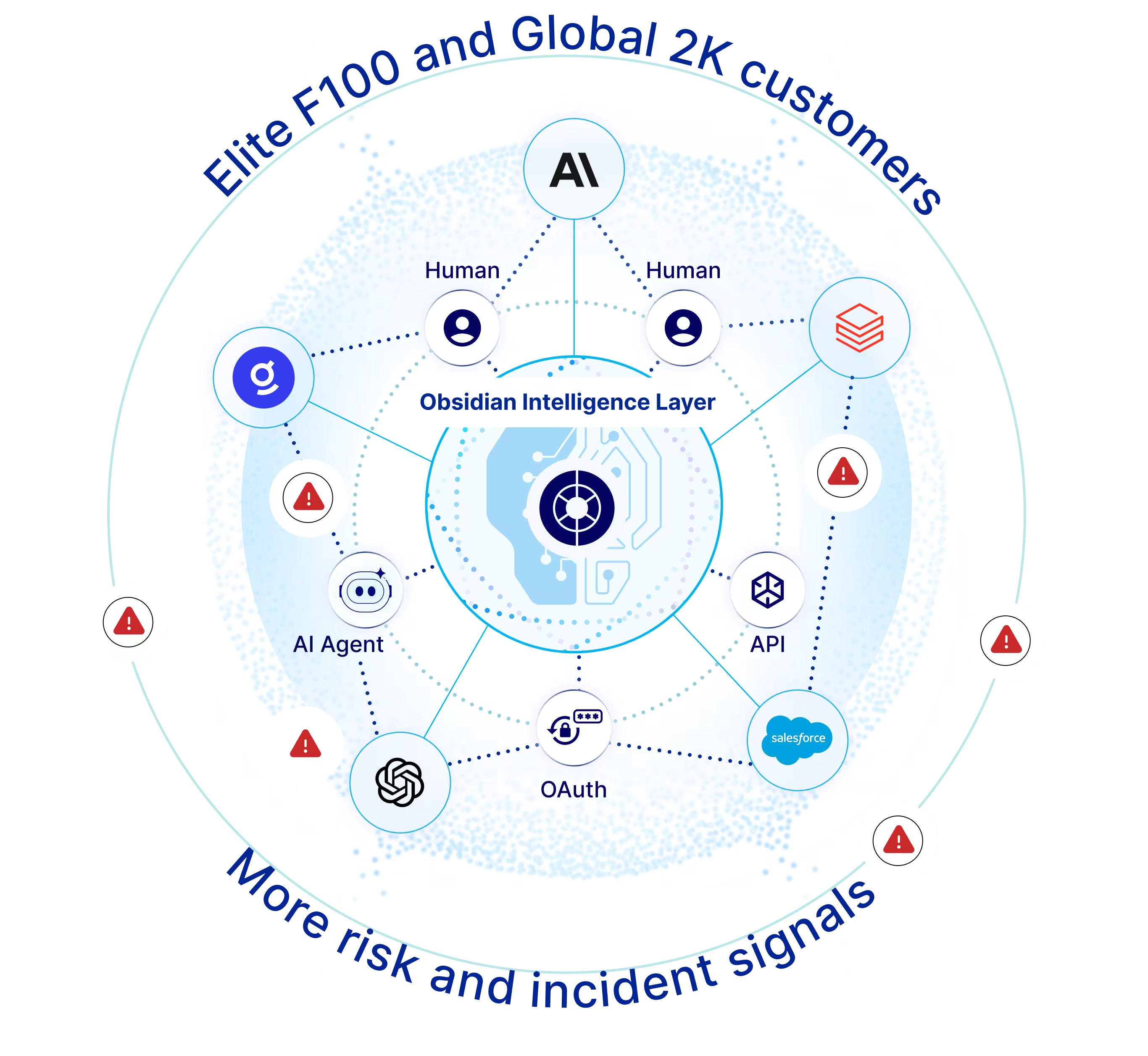
The Obsidian Intelligence Layer learns from every environment we protect. When a threat surfaces anywhere in our network, every customer is already defended.
Events processed monthly
Scale of deployments
Breach responses