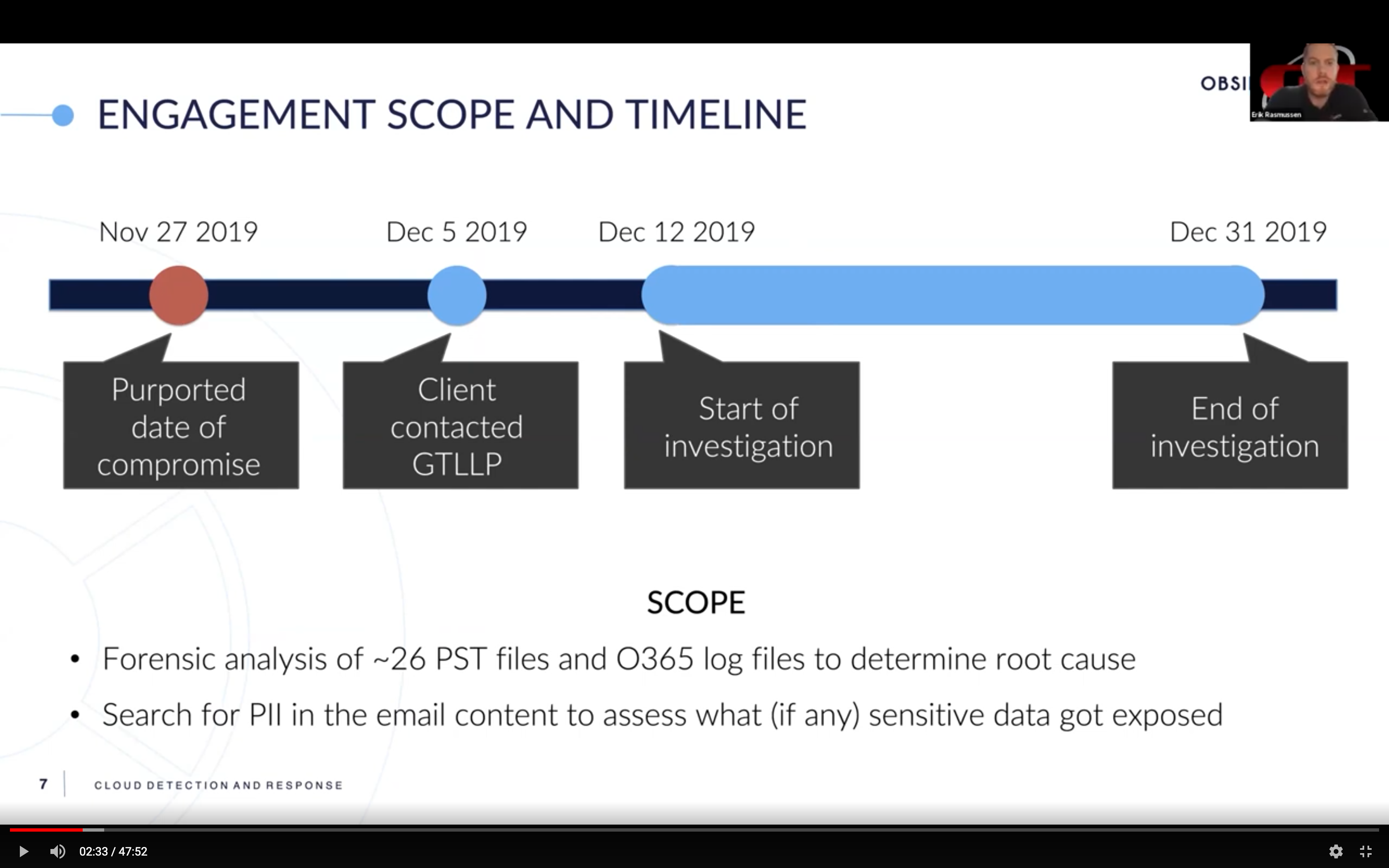
I recently spoke with Erik Rasmussen, principal and head of cybersecurity and risk management solutions at Grobstein Teeple LLP about how his team investigated an email account compromise at a law firm. Business email compromise (BEC) costs organizations billions of dollars in losses. A previous blog post went over the case timeline and investigation steps. If you haven’t read that post yet, it’s a great place to start.
Let’s now look at security practices and tools that Erik recommends to protect against business email compromise and how to quickly respond to an incident. The recommendations fall into three areas:
- Reducing the likelihood of BEC
- Preparing for Response
- Responding to BEC
Reducing the Likelihood of Compromise
Protecting against BEC is primarily about controls that you have in your environment.
- Use the in-flight encryption capabilities of the underlying email platform to protect data in transit. Microsoft Office 365 and G Suite both offer confidentiality capabilities to encrypt data; e.g., Google Confidential. Learn about it, and use it.
- Make sure that all email accounts have multi-factor authentication (MFA) enabled. MFA is a simple yet often overlooked security measure for protecting accounts.
- For financial transactions such as wire transfers, use a control mechanism like the two-man rule. The wire transfer sender has to call or visually verify the request before making the transfer.
- Don’t send passwords in email. Some applications share passwords with new users via email. In these cases, have a policy to change the password on first use.
- Don’t share sensitive documents via email. Have collaborators go to a secure server or file share with a unique URL and its own MFA.
Preparing to Respond Better
In addition to deploying security controls to prevent BEC, security teams should adopt a posture that allows them to respond quickly if/when an incident occurs.
- Have a way to communicate with the affected users outside of email if the email channel is compromised.
- Have logging turned on and export the access audit log to an external location in case it is to be lost during the attack. This can be done continuously or periodically.
- Have backup protocols in place so you can restore deleted or encrypted email.
- To the extent that budget allows, have an IR retainer with clearly understood SLAs.
- Have a game plan for who does what when an incident occurs. If you have an IR firm on retainer, this extends to the IR team as well. Practice your roles and responsibilities so you are ready.
- Look for telltale signs of risky and suspicious activity; e.g.,
- Mail forwarding to/from personal accounts
- Files being accessed anomalously
- Editing of email logs
Responding Quickly to Account Compromise
Time is of the essence in responding to incidents. You need to stop the bleeding and restore productivity as quickly as possible.
- Quickly ascertain the scope of the incident so you don’t boil the ocean. How many mailboxes or accounts have been potentially compromised? What is the timeframe of data stored in the mailbox?
- If there was a data breach, find out what data was exposed. Depending on the nature of the data, it may necessitate data breach notification depending on where the data was sitting, where the firm was operating, and what users or clients were in the data pool.
- Understand the attacker’s intent. Just because somebody accessed the email account, it doesn’t mean they accessed the data. Sometimes all attackers want is access to the email account so that they can send out phishing emails for money transfer.
- Speed of data analytics and data retrieval is key. Get the data you need to analyze the situation either using an in-house solution or a security tool.
- Start taking recovery steps you can while you investigate; e.g., change passwords, restore data from backups, enable MFA.
You can watch the entire webcast here. I thank Erik for shining a light on how IR firms and organizations investigate and respond to email compromise incidents. We are proud to partner with GTLLP to help customers stay secure in their SaaS environments.
We’ll leave you with these final thoughts. Cloud email is no longer just a communication tool, but a virtually unlimited repository for employees to store, search and share data easily. Implement strong security controls (MFA, two-man rule) and use the native security capabilities of your cloud email solution such as data encryption to reduce the likelihood of compromise. Be prepared to respond quickly if an account gets compromised.
If you’re interested in learning more about how Obsidian can help, get a demo or drop us a note.