Solution
HYGIENE & ACCOUNT RIGHT-SIZING
SECURE BORDERLESS ENVIRONMENTS
THE BATTLEGROUND HAS SHIFTED
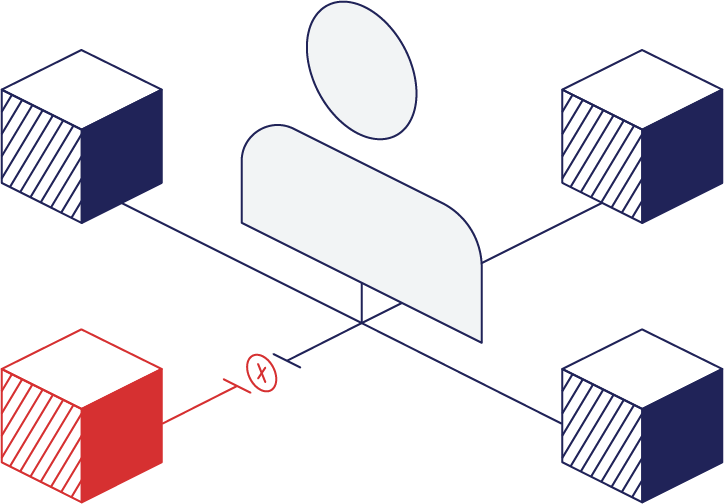
The traditional model of enterprise security built to protect networks and endpoints is no longer sufficient. Rapid proliferation of cloud services, IoT, and mobile workers has dramatically changed the attackable surface area. Organizations now rely on granular control over user identities to ensure that the right applications are accessed by the right people for the right purposes at the right time to establish Zero Trust architectures. This is the new identity perimeter.
VISIBILITY AND RISK MONITORING
CENTRALIZED IDENTITY DATA ENHANCES RISK INFERENCE
Obsidian provides a single source of trust for identity and access, allowing security administrators to answer key questions around who has access to which resources, what they are doing with their privileges, and what actions can be taken to improve the organization’s risk profile. For the first time, security operations, identity governance and incident response teams have a shared view of the people they are defending.
INCIDENT RESPONSE AND FORENSICS
COMPROMISED CREDENTIALS, INSIDER THREATS, AND SUSPICIOUS BEHAVIOR
Obsidian enables a new paradigm in incident response. Hunters and Incident responders can use Obsidian to get rich context built around identities and access, allowing them to effectively investigate suspicious activities and abnormal behavior. Incident responders have a single, consolidated view into the timeline of activity for a user, the entire organization, or anything in between. The identity data model is accessible via the web UI as well as through the powerful GraphQL API. It is your data, and you have it your way.
Finally, security operations teams who need quick triage, or incident response consultancies who need to parachute in to stop the bleeding, benefit from instant onboarding, data collection, and export capabilities.
IDENTITY LIFECYCLE MANAGEMENT
Obsidian’s Identity Graph enables continuous account monitoring and privilege auditing
Obsidian provides contextual intelligence to make data-driven decisions about the permissions assigned to each person and role. This is useful for provisioning, de-provisioning and pruning privileges and identities to improve security by minimizing the attack surface.
Obsidian changes attestation from a manual human driven process to one enabled by the Obsidian Identity Graph. The advantage of Zero Trust architectures is finally within reach.