


The NIST Cybersecurity Framework has been one of the most widely adopted models for assessing and managing cybersecurity risk in private organizations since its introduction in 2014. A key strength of the framework, originally intended to protect critical infrastructure, is its versatility. If you are a security leader trying to understand, catalog and protect against risks and threats in new environments, the model can help with this.

As organizations ramp up their consumption of SaaS and the public cloud, the threat landscape is also shifting. Identity is an important perimeter as well as vector of attack in the cloud. The identity perimeter is the collection of users (and service accounts) and digital assets in the organization, and the access relationships between them. In this post, we look at how security leaders can apply the NIST Cybersecurity Framework to develop an approach for protecting users and their access to the organization’s digital assets.
The NIST Cybersecurity Framework describes five functions that work in tandem to help organizations protecting digital assets:
Let us now look at how these core functions apply to protecting identities in a multi-cloud environment.
Function
Identify
Protect
Detect
Respond
Recover
Get visibility into all the accounts that a user (or robotic identity) has across cloud services, as well as privileges associated with each user in these servicesExamine how cloud services such as Salesforce, Dropbox, G Suite, and AWS are configured to understand the overall cloud security posture and service risk levelEstablish which identities are privileged and which are high-value targets in your organization. For example, service accounts used for automation in AWS environments have a concentration of privileges that make them valuable to attackers
Maintain the principle of least privilege by starting with zero-trust and assign access based on what is neededConduct regular access reviews to ensure that a user’s access and privileges conform to organizational policyRight-size access and privileges on an ongoing basis and remove unused accounts and entitlementsEnforce best practices around identity management and authentication — enable multi-factor authentication (MFA), deploy single sign-on, stipulate password policies, enable adaptive access controlDetect and reverse application and service configuration drift
Establish continuous observability of activity across cloud services with context around which identities are performing the actionsDetect account takeover and insider threat based on user behavior analyticsConduct threat hunting using the consolidated activity stream to find threats and automate detections
Investigate incidents and threats with full visibility into what users did and accessedEstablish an audit trail that can be used for evidence gathering, investigation, and reporting
Update training and tooling to prevent or detect similar incidents from recurringVerify that passwords have been reset and other activities indicative of a successful response have been completedBuild automated detections that provide early warning against threatsRestore affected services, remove backdoor accounts, and revert configuration changes
Obsidian offers a new approach to protect SaaS, PaaS and IaaS environments from account takeover, insider threat and identity sprawl. Obsidian continuously monitors activity, access and entitlements to provide a holistic view of threats and risks at the user, organization, and application levels. Customers see prioritized alerts that surface the most pressing security and posture concerns in the cloud.
To better explain what Obsidian offers, let’s see how Obsidian’s capabilities map to the NIST framework.
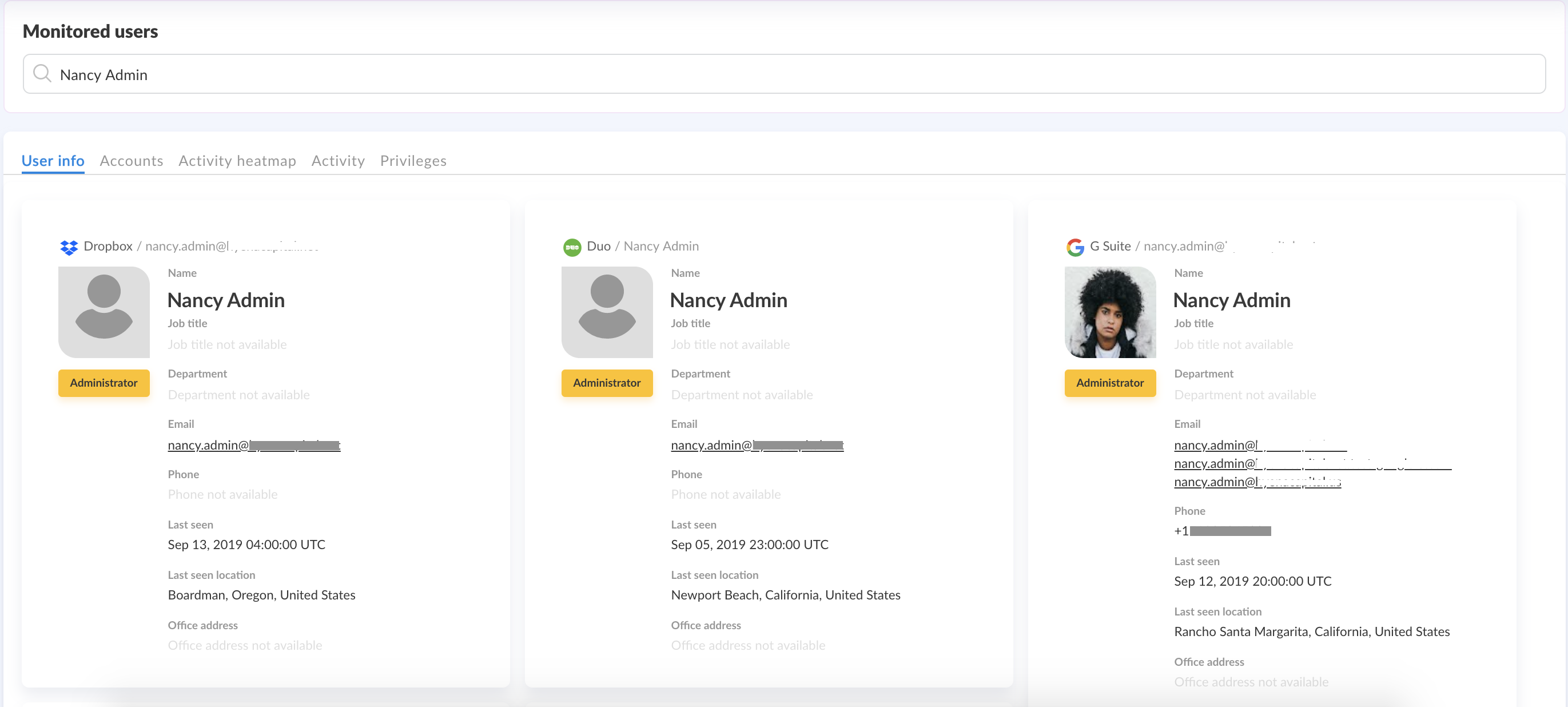
Obsidian allows security teams to see who their cloud users are, and what accounts and privileges they have across cloud services. Rather than just showing a collection of accounts in each service, Obsidian resolves accounts belonging to a particular user or identity, and provides visibility into the identity footprint of each user. The platform shows whether a user has administrative privileges or roles in any service.
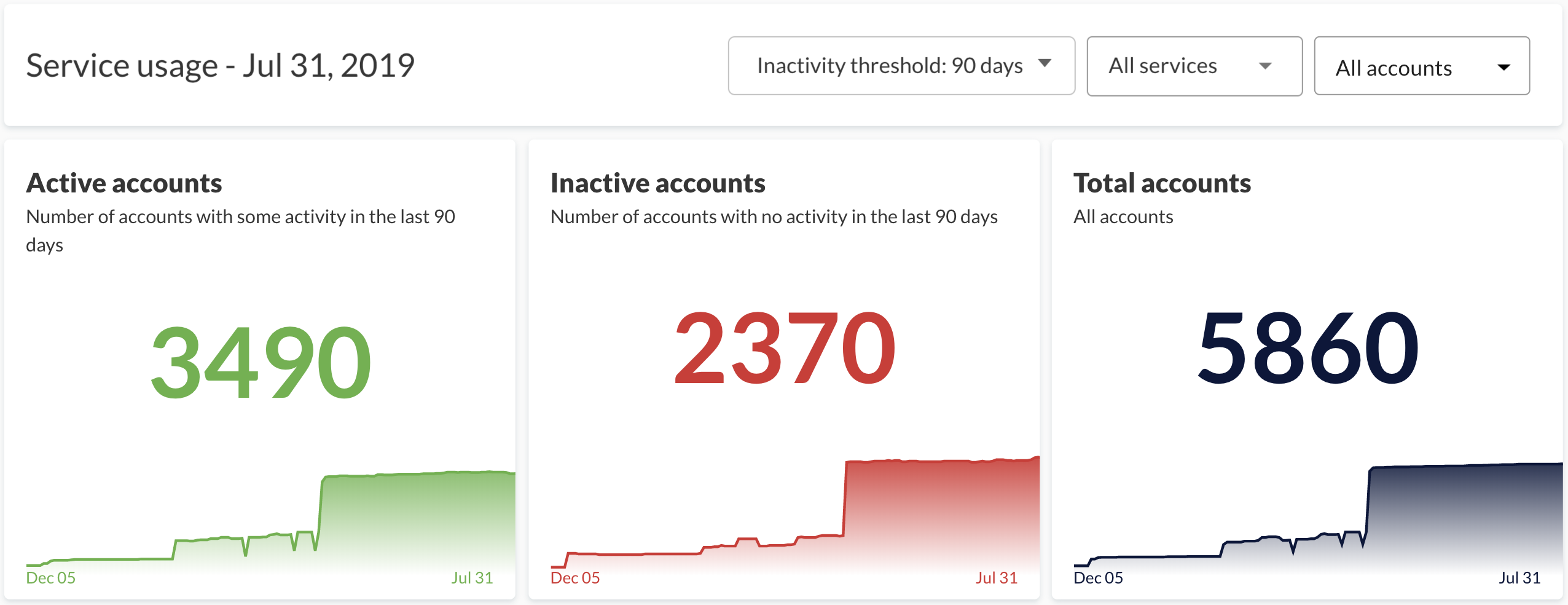
Using Obsidian, IT ops and security teams can conduct regular access reviews and identify accounts and privileges that are unused across services. Pruning inactive accounts and fixing common application misconfigurations reduces risk. A lower risk profile not only reduces the chance of a costly breach, but also lowers the indirect costs of ongoing security efforts.
Obsidian helps SOC teams detect account compromise and insider threat early in cloud applications and services by continuously monitoring and analyzing activity. Security teams get alerts about inappropriate access and risky user behavior, allowing them to respond quickly. By automatically prioritizing alerts, Obsidian helps security teams mitigate alert fatigue by focusing on the biggest risks and threats to the organization’s security. Alerts inform security teams and managers in the organization about suspicious activity and abnormal behavior.
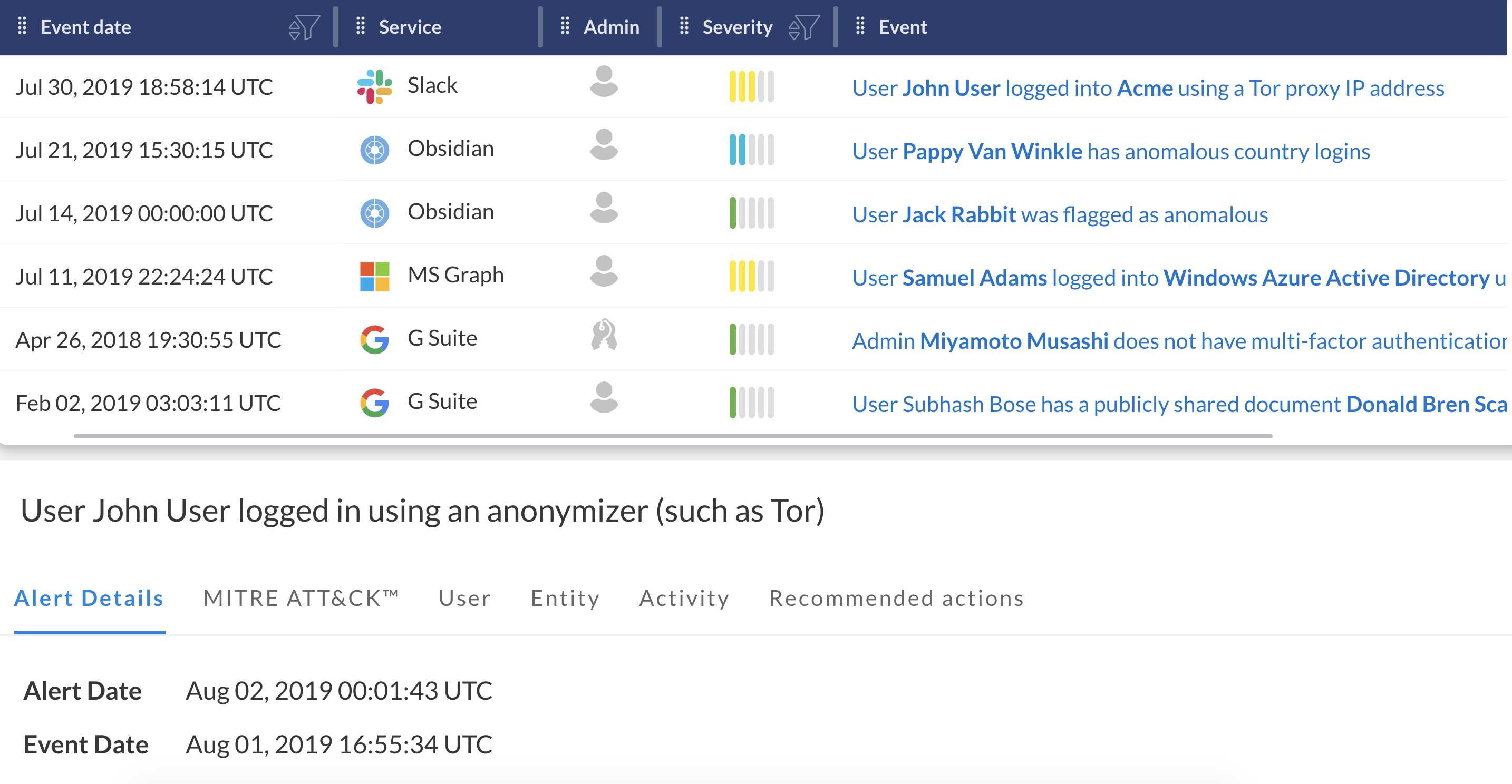
Obsidian offers rich out-of-the-box alerts to detect a wide range of threats without any configuration required. Are employees downloading an unusual amount of data from Salesforce? Sharing key documents with the entire internet? Logging in using a Tor browser? Are you seeing an alarming number of unsuccessful logins on a particular account? How about logins from an unfamiliar geo? Obsidian alerts cover well known malicious posturing and attempted attacks, and are sorted by severity level.
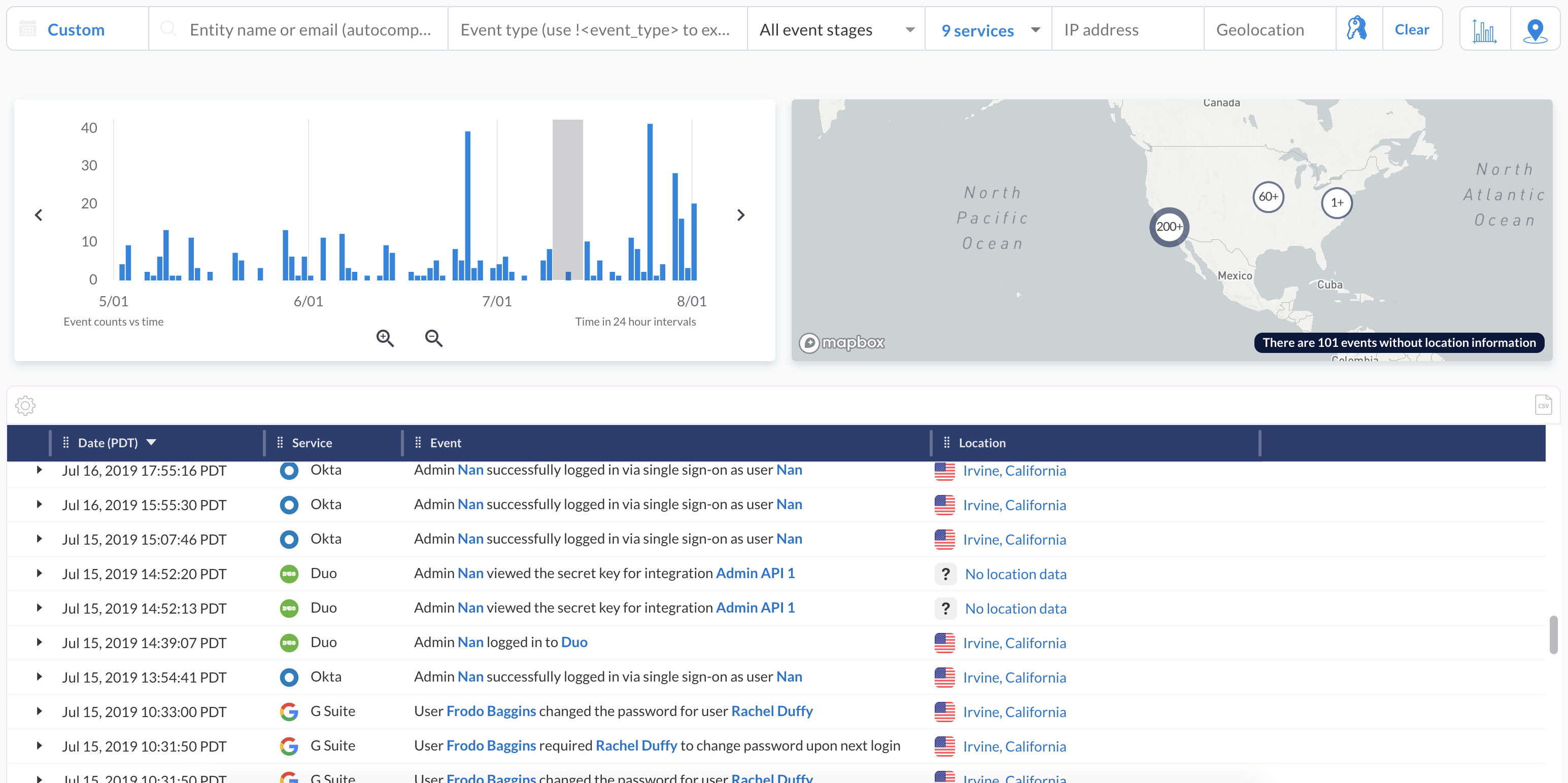
Using Obsidian, security teams can investigate incidents and threats with a consolidated activity stream. With an understanding that IP addresses are not identities, Obsidian’s activity view provides rich context into what users did when, from where, and using what devices. The Obsidian activity view is like a Flight Data Recorder for cloud services.
Obsidian offers remediation recommendations in the context of each alert to guide successful response.
The traditional model of enterprise security built to protect networks and endpoints is insufficient. The rapid proliferation of cloud services, IoT, and mobile workers has dramatically changed the attackable surface area and introduced new threats. Security teams need to continuously monitor permissions and activity at a granular level to ensure that their companies’ digital assets are secure.
In an era where appropriate access management is the final line of defense against hackers and malicious actors, security posture management and threat detection capabilities need an overhaul. The NIST Cybersecurity Framework is relevant and useful for security leaders to understand, and can inform the building of a comprehensive defense strategy against cloud threats.
To find out how Obsidian can help you manage access for non-employees in your organization better, drop us at note at general@obsidiansecurity.com or sign up for a demo at www.obsidiansecurity.com.
Start in minutes and secure your critical SaaS applications with continuous monitoring and data-driven insights.