Normalize
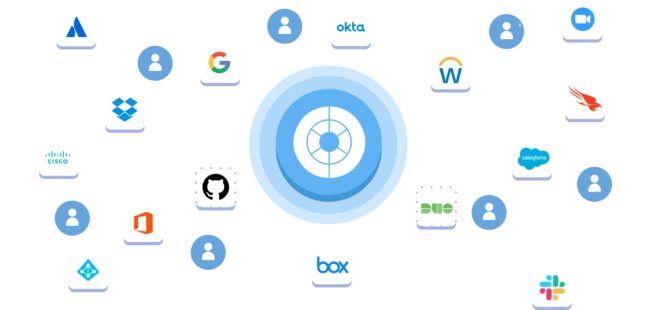
Obsidian maps complex data schemas across SaaS applications using inputs from hundreds of APIs and various protocols. We maintain these connections through vendor outages and upgrades, ensuring API drift and stability doesn’t compromise data integrity. We then retrieve and normalize large volumes of data across your applications, resolve accounts to identities, and add threat intel and context. The result is a proprietary knowledge graph that provides an excellent baseline for threat detection.

Model
All activity is interpreted with machine learning and statistical analysis to detect account compromise, insider threats, data leaks, and risky behavior. These models are continually refined by data from our diverse customer base, resulting in a more accurate model than any one environment can provide. From the knowledge graph, we’re able to identify anomalous activity with a high degree of accuracy.

Operationalize
Outputs from our advanced detection models deliver actionable, high-fidelity recommendations. We use the normalized data in our knowledge graphs to reveal exactly how changes will impact users in your environment, enabling your security team to act swiftly and with confidence. Our logs can be incorporated into existing workflows via downstream integrations with your SIEM or SOAR. Obsidian delivers outcomes, not just alerts.